The most overlooked and underestimated part of cyber incident response planning
Assessing compromised data following a data breach is often the most complex, costly, time-consuming and stressful part of any incident response. Delays or errors in data assessments and notifications can provoke customer backlash, regulatory scrutiny and unwanted media attention, causing significant reputational and legal exposure.
Yet assessing compromised data is also the most overlooked and underestimated part of incident response planning. No single technology can deliver fast, defensible data breach analysis on its own. Effective outcomes require the right mix of technologies, tailored processes and experienced legal oversight.
RADAR (Response and Data Assessment Review) provides this integrated solution—combining legal expertise, purpose-built technology and proven workflows to deliver fast, defensible and cost-effective data breach assessments.
Key features
|
Trusted expertise and judgement Our team of leading cyber, privacy, digital and data experts brings decades of breach response and regulatory investigation experience. This expertise helps us efficiently narrow the dataset for detailed review, and assess data to inform your notification strategy—quickly, pragmatically and defensibly. |
|
 |
Purpose-built, multiplatform offering - Pairing expert guidance with leading technologies and tailored workflows We've invested in a suite of market leading technologies so you don't have to. Rather than relying on one tool to do it all, we combine expert guidance with the right mix of technologies and tailored workflows. This ensures the solution fits your specific breach, not the other way round. Our approach integrates Canopy’s proven compromised data workflows with additional tools to tackle specific data challenges1, whether that’s unstructured data, large spreadsheets, images, audio/video files, foreign language content or restricted datasets (eg suspicious matter reporting information). |
|
Scalable and AI-powered - For faster, more accurate data assessments and notifications Unlike traditional tools which use data mining methods (eg keywords, regular expressions and pattern matching), we leverage Canopy’s AI driven breach assessment engine. This is purpose built to rapidly identify personal information and link it to affected individuals, even across complex data types, with appropriate levels of human oversight for accuracy. |
|
 |
Secured All platforms in RADAR are ISO 27001 certified and aligned with SOC 2 Type 2 requirements. Data is hosted in Australia within dedicated Allens instances, encrypted both at rest and in transit. Access is tightly controlled through multi factor authentication and/or single sign on, with strict user access protocols. User activity and document access is tracked and logged for auditability. |
|
Custom reporting - Providing you with visibility, control and assisting with stakeholder management From the earliest stage of assessment, we generate tailored reports outlining review progress and data attributes identified in the dataset that may impact the review and notification strategy. These reports help you keep internal and external stakeholders informed, manage board and insurer expectations, and meet regulatory notification requirements. |
Why eDiscovery platforms alone aren't the answer
eDiscovery tools excel at litigation review, but fall short for compromised data assessment because they:
- lack advanced analytics to accurately identify personal information across diverse formats.
- struggle to link individuals with their personal information, especially across multiple documents and in large, unstructured datasets.
- add complexity, cost and time when creating custom reports and notification lists.
When to use RADAR
Cyber incidents involving data theft or unauthorised access
Accidental data breaches
Insider threats
Unauthorised employee access to data
Personal information access requests
How it works
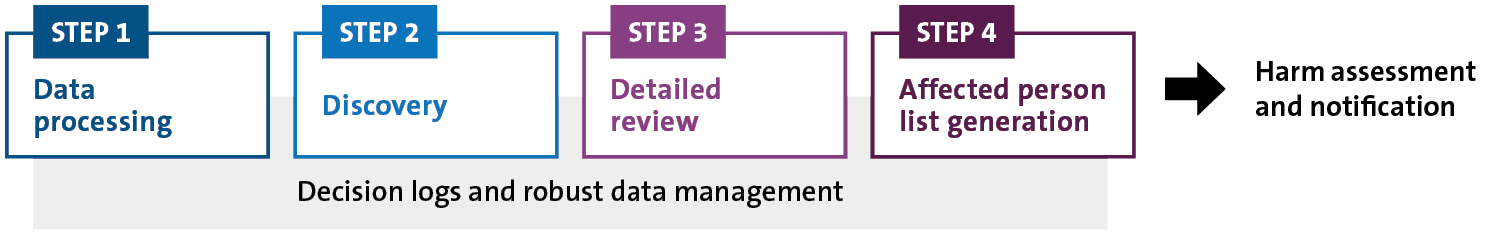
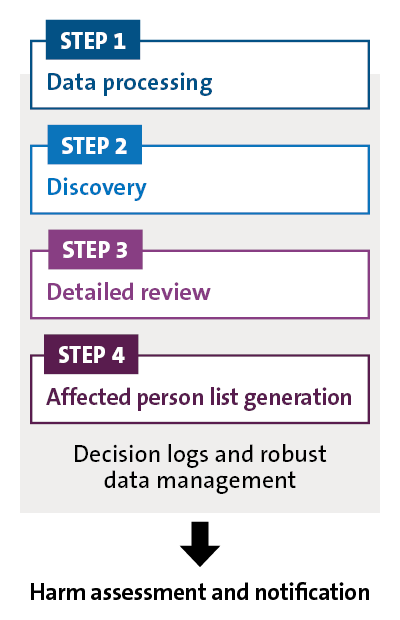
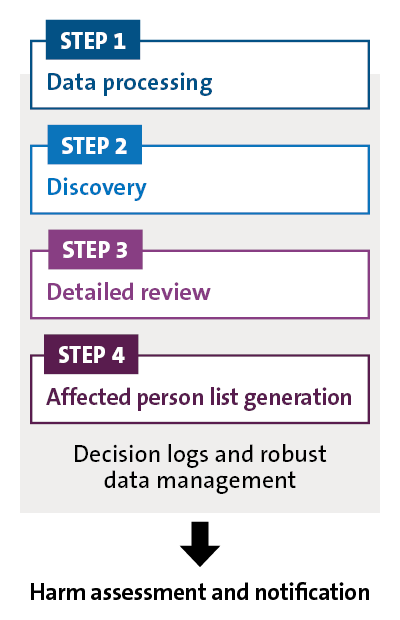
Technology platforms

Canopy
Canopy delivers an end-to-end data breach assessment workflow, from early insights and AI-enhanced document review to detailed reporting on affected individuals.

Reveal
Reveal analyses complex, non-standard file types using advanced AI and custom detection models for nuanced PI identification.

NUIX Workstation
A highly customised data-processing platform for targeted search and advanced document-volume reduction.

Legora
Provides a GenAI powered workspace to summarise, extract and review affected documents.
Why choose Allens
Trusted expertise and defensibility
Our team of leading cyber, privacy, digital and data specialists brings decades of breach response and regulatory investigation experience. This expertise (combined with our purpose-built, multiplatform offering) helps us narrow the dataset for detailed review, and assess the data to inform your notification strategy—quickly, pragmatically and defensibly. Our proven methodology includes an audit trail and decision logs that build confidence with boards and withstand regulatory scrutiny.
Risk, reputational and stakeholder management
We guide you through the entire process, providing visibility and support throughout. We prioritise the highest risk, most sensitive datasets and notifications, helping you mitigate impact and manage relationships with customers, boards, regulators and media.
Cost predictability
Transparent pricing with pre-agreed fixed fee components helps you budget effectively, brief insurers, and manage costs while moving quickly.
Expert review capabilities
Our tailored workflows, quality controls and right sized review teams (supervised by Allens lawyers) accelerate the initial assessment, to help refine response strategies while managing time and cost
Continuous improvement
We refine RADAR after every incident, drawing on fresh insights and best in class tools to ensure your response adapts to evolving regulatory expectations and technical capabilities.
Footnotes
-
In addition to Canopy, tools currently include Legora, Nuix Workstation, Nuix Discover, Reveal, RelativityOne, Microsoft Foundry and Python.